
Build strong IT policies for compliance and efficiency
TL;DR:
- Strong IT policies are essential for risk reduction, regulatory compliance, and operational efficiency.
- Clear distinction between policies, standards, procedures, and guidelines ensures effective cybersecurity governance.
- Ongoing review, enforcement, and stakeholder engagement are crucial for policies to deliver real organizational value.
Most mid-sized engineering and finance firms do not lose data because hackers are clever. They lose it because nobody wrote down who can access what, or the policy document sits forgotten on a shared drive. IT policies form the foundation of cybersecurity programs, ensuring consistent procedures across organisations. Yet most firms treat policy development as a once-off exercise rather than a living system. This guide walks you through the frameworks, terminology, and lifecycle steps that turn vague policy documents into genuine compliance assets and operational efficiency tools your team will actually follow.
Key Takeaways
| Point | Details |
|---|---|
| Policies reduce breach risk | Strong IT policies significantly lower the likelihood of security incidents and compliance failures. |
| Policy pyramid drives clarity | Understanding the difference between policies, procedures, standards, and guidelines simplifies compliance and enforcement. |
| Frameworks enable efficiency | Mapping policies to NIST, ISO, CIS, and COBIT improves operational effectiveness and regulatory readiness. |
| Review and adapt regularly | Annual policy reviews and real-time updates keep firms compliant and resilient to emerging threats. |
| ROI comes from action | IT policies must be actively used, audited, and improved to deliver measurable returns. |
Why IT policy matters for mid-sized firms
Engineering consultancies and financial advisory firms sit in a difficult position. They handle sensitive client data, face sector-specific regulations, and yet rarely have the internal IT headcount of a large enterprise. This is exactly where strong IT policy development pays off most.
Consider what a policy framework actually protects against. The majority of cybersecurity incidents trace back to governance failures, not sophisticated zero-day exploits. When staff share credentials, use personal devices without rules, or transfer client files through unapproved channels, the breach waiting to happen is a policy gap. IT policies form the foundation of cybersecurity programs, particularly vital for mid-sized firms handling sensitive engineering and finance data.
For firms exploring innovative IT solutions, policy development is the starting point that makes every other investment worthwhile. You cannot secure what you have not defined.
Here is what strong IT policy delivers practically:
- Risk reduction: Clear access controls and acceptable use policies close the most common breach vectors before attackers even look for them.
- Regulatory alignment: Finance firms face FSCA and POPIA obligations; engineering firms face sector-specific data handling rules. Documented policies prove compliance during audits.
- Operational consistency: When staff know the rules, IT support spends less time firefighting and more time on value-adding work.
- Scalable IT operations: Policies that are written properly scale with your headcount without needing constant rewrites.
The IT service management benefits of a policy-first approach include measurably faster incident response and lower average cost per breach. For IT support for financial services firms, this translates directly to regulatory confidence. For IT support for engineering firms, it means protecting proprietary project data and client deliverables.
“A policy document that no one reads is not a policy. It is a liability shield that offers no actual protection.”
The firms that get the most from protecting your company through IT governance are those that treat policies as operational tools, reviewed regularly and communicated clearly to all staff.
Understanding the policy pyramid: Standards, procedures, and guidelines
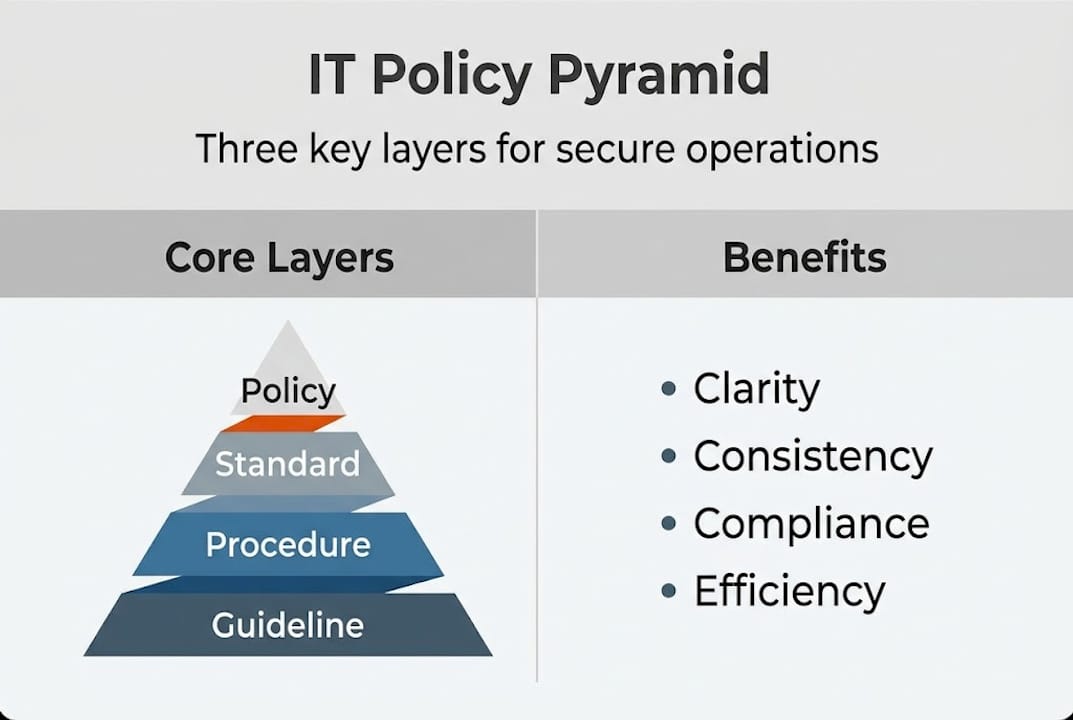
One of the most common mistakes IT managers make is confusing policies with procedures. They are not the same thing, and treating them interchangeably creates documents that are either too vague to act on or too prescriptive to remain useful as the business evolves.
The Policy Pyramid gives you a clear mental model:
- Policies define what must be done and why. Example: “All company data must be encrypted at rest.”
- Standards specify the minimum requirements for achieving the policy. Example: “AES-256 encryption is the minimum standard.”
- Procedures explain how the standard is implemented step by step. Example: “Follow these six steps to enable encryption on a new endpoint.”
- Guidelines offer recommended best practices that are advisory rather than mandatory. Example: “Consider enabling full-disk encryption on contractor devices as well.”
Here is a quick comparison to keep these clear:
| Layer | Answers | Mandatory? | Example |
|---|---|---|---|
| Policy | What and why | Yes | Acceptable use policy |
| Standard | Minimum requirements | Yes | Password length of 14 characters |
| Procedure | Step-by-step how | Yes | Onboarding access provisioning steps |
| Guideline | Best practice advice | No | Recommended VPN usage for remote work |
Evolving cybersecurity policies in 2025 and beyond require IT managers to keep these layers distinct, because regulators increasingly audit the connection between a stated policy and the procedure that enforces it.
Good IT documentation best practices start with building this hierarchy before writing a single word of policy content. Structure first, then content.
Pro Tip: AI tools like Microsoft Copilot or ChatGPT can draft initial policy language quickly. Use them to generate a first draft based on your chosen framework, then have your IT manager or legal counsel review for sector-specific compliance gaps. AI speeds up the drafting phase significantly but cannot replace contextual human judgment. See how AI in cybersecurity is changing how firms approach both threat detection and documentation.
Choosing the right framework: NIST CSF, ISO, CIS, and COBIT
Choosing a framework is less about picking the “best” one and more about understanding which combination fits your firm’s regulatory environment, risk appetite, and available resources.
NIST CSF 2.0 introduces a Govern function specifically designed to embed policy development into enterprise risk management. This is particularly useful for firms that need to demonstrate cybersecurity maturity to clients or regulators without pursuing formal certification.
Here is how the four major frameworks compare:
| Framework | Approach | Best for | Certification? |
|---|---|---|---|
| NIST CSF 2.0 | Flexible, outcome-based | Risk management alignment | No |
| ISO 27001 | Process-heavy, certifiable | Firms requiring formal audit proof | Yes |
| CIS Controls | Prioritised, practical | Quick wins for under-resourced teams | No |
| COBIT | Governance-focused, comprehensive | IT governance and board reporting | Partial |
Hybrid approaches are recommended for compliance efficiency because no single framework covers every requirement. A practical starting point for mid-sized firms:
- Map your core policies to NIST CSF 2.0 Govern and Protect functions.
- Use CIS IG1 controls as your minimum implementation checklist.
- Apply ISO 27001 clauses where client contracts or regulatory requirements demand it.
- Use COBIT principles for board-level IT governance reporting.
Regulatory pressure is rising. NIS2 in Europe and SEC cybersecurity disclosure rules in the US are pushing annual policy reviews into mandatory territory for firms with cross-border exposure. Firms operating in South Africa must also align with POPIA and financial sector cyber resilience guidance from the SARB. Reviewing cybersecurity best practices annually is no longer optional for regulated industries.
Stat callout: Firms that align IT policies to a recognised framework reduce audit preparation time by up to 40% and demonstrate measurably lower incident rates over three-year periods.
Policy lifecycle: Drafting, approval, review, and continuous improvement
A policy that gets written once and never touched again is one of the most dangerous documents in your organisation. It creates a false sense of security while the real environment moves on without it.
Here is the lifecycle that works for mid-sized firms:
- Draft: Use the Policy Pyramid structure. Assign a policy owner for each document. Use AI in cybersecurity policy drafting tools to generate initial language, then adapt it to your firm’s context.
- Stakeholder review: Circulate drafts to department heads, legal, HR, and your IT team. Policies that skip this step get ignored in practice because staff feel no ownership.
- Formal approval: Document sign-off from the appropriate authority, whether that is the IT director, CFO, or board depending on the policy’s scope.
- Communicate and train: A policy only works if staff know it exists and understand what it requires of them. Brief trainings and accessible policy summaries are essential.
- Enforce and monitor: Use your IT systems to enforce where possible. Password policies enforced by Active Directory are far more reliable than ones that rely on individual compliance.
- Review and improve: Schedule annual reviews as a fixed calendar item. Trigger unscheduled reviews after any significant incident, regulatory change, or major infrastructure shift.
Annual reviews post-NIS2 and SEC rules are becoming baseline expectations. The NIST Quick-Start Guide aids workforce planning and risk communication throughout this lifecycle.
Pro Tip: Track measurable outcomes against your policies. Metrics like mean time to detect an incident, number of policy exceptions granted, and staff compliance rates during phishing simulations give you tangible ROI data. Your IT security audit checklist should include policy compliance as a scored item, not just a checkbox. Firms investing in structured policy management often find, as cybersecurity analyst roles evolve, that documented policies reduce analyst onboarding time and incident response ambiguity significantly.
Why most policy efforts fail—and how to get real ROI
After working with engineering and finance firms across a range of sizes, the pattern is remarkably consistent. The policy document exists. It was written carefully, maybe even reviewed by a consultant. And then nothing happens. No training, no enforcement, no follow-up review.
The uncomfortable truth is that most IT policy failures are not technical failures. They are communication and accountability failures. Policies live in a folder, not in the daily decisions of your staff.
Cumulative governance failures cause over 80% of incidents. The firms that genuinely reduce breach risk are those that build policy compliance into onboarding, annual reviews, and system configurations simultaneously.
Real ROI from IT policy development comes from three things. First, policies that are written at the right level of specificity, not so vague they mean nothing and not so detailed they become obsolete in six months. Second, enforcement mechanisms that are built into your systems rather than relying on human memory. Third, a review cycle that is owned by a named person, not a committee that never meets.
Focus on preventing data loss through policy enforcement rather than reactive incident response. The firms that do this consistently spend less time in crisis mode and more time on billable work.
Get expert IT help for streamlined policy management
Developing and maintaining IT policies is not a once-off project. It is an ongoing governance function that requires structured support, good documentation habits, and regular technical review. At Techtron, we help mid-sized engineering and finance firms build policy frameworks that are actually enforced, not just filed away.
Our team supports everything from IT documentation best practices to full infrastructure governance reviews. If you are navigating cybersecurity in South Africa and need to align with POPIA or sector-specific requirements, we provide practical guidance tailored to your firm’s scale. Explore our IT infrastructure management strategies or contact us directly to discuss a policy review engagement that fits your team and budget.
Frequently asked questions
What is the difference between IT policies and procedures?
IT policies describe the high-level “what” and “why” of expected behaviour, while procedures explain step-by-step “how” each policy is implemented in practice. Keeping these distinct layers clear prevents documents that are either too vague or too rigid to be useful.
Which framework is best for IT policy development in mid-sized firms?
No single framework covers everything. A hybrid approach combining NIST CSF for risk alignment, CIS Controls for practical implementation, and ISO 27001 clauses where certification is needed offers the best compliance and operational fit for mid-sized engineering and finance firms.
How often should IT policies be reviewed and updated?
IT policies should be formally reviewed at least annually and updated promptly after major incidents or regulatory changes. Annual reviews are increasingly a baseline expectation under NIS2 and SEC cybersecurity disclosure rules.
Can AI be used to draft IT policies?
AI tools can generate solid first drafts based on your chosen framework quickly, but human review is critical to ensure the final policy reflects your sector’s compliance requirements and your firm’s actual operating context.