03/04/20
Security Best Practices While Working From Home
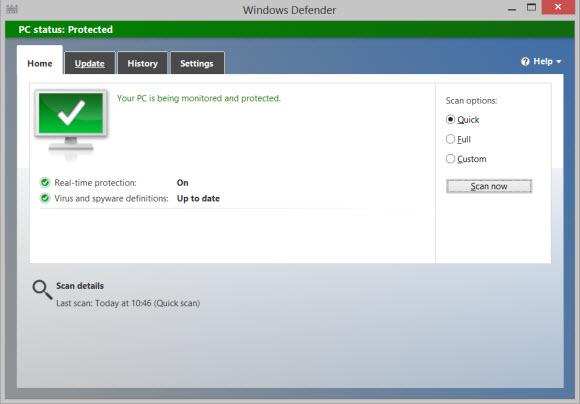
While COVID-19 continues to aggressively spread across the globe, many employees worldwide are facing the realities of working remotely for the first time. Simultaneously, there is increasing evidence to show that malicious actors are using concerns of the virus to prey on those same individuals. Given this, it is more important than ever before that employees understand their role in protecting their...
Read More