
Network Vulnerability Assessments: Reducing Business Risk
Securing your network often feels like a moving target, especially when compliance stakes are high for South African engineering and financial firms. Cyber threats evolve daily and hidden weaknesses can leave your infrastructure exposed where it matters most. A systematic vulnerability assessment provides clear visibility into these risks, identifying both physical and logical gaps before attackers or regulators discover them. Gain practical steps to fortify your systems and meet POPIA requirements with confidence.
Key Takeaways
| Point | Details |
|---|---|
| Network Vulnerability Assessments Identify Weaknesses | These assessments systematically locate security vulnerabilities in IT infrastructures, helping organisations preempt attacks. |
| Structured Assessment Methodology | The assessment process includes scanning, testing configurations, and providing detailed remediation reports tailored to organisational needs. |
| Both Physical and Logical Vulnerabilities Matter | Assessments must consider unsecured physical locations as well as software flaws, especially in sensitive industries like finance and engineering. |
| Compliance and Risk Management Support | Regular assessments reinforce compliance with regulations like POPIA, proving proactive security measures to regulators and reducing risk. |
Defining Network Vulnerability Assessments
A network vulnerability assessment is a systematic process to identify, classify, and document security weaknesses in your IT infrastructure. Think of it as a health check for your network—it scans your systems, servers, and devices to find where attackers could potentially break in.
For mid-sized engineering and financial firms in South Africa, this means examining everything from firewalls and routers to workstations and databases. The goal is simple: find problems before criminals do.
What Happens During an Assessment
Network vulnerability assessments follow a structured methodology. The process includes:
- Scanning network devices and systems for known weaknesses
- Testing configurations to identify misaligned security settings
- Classifying findings by severity and potential business impact
- Delivering detailed reports with specific remediation advice
According to the South African National Research Network, vulnerability assessments identify security weaknesses in IT infrastructure and provide actionable recommendations for strengthening your network security posture.
Your team receives more than just a list of problems. You get verified results showing exactly which vulnerabilities exist, where they’re located, and what you need to do about them.
Physical and Logical Vulnerabilities
Assessments examine both types of weaknesses. Physical vulnerabilities might include unsecured server rooms or damaged network cables. Logical vulnerabilities involve software flaws, misconfigured permissions, or outdated systems.

For financial firms handling sensitive client data, logical vulnerabilities pose the greater risk. For engineering companies with proprietary designs, both types matter equally.
An assessment captures the full picture of your security posture across hosts and network infrastructure.
To clarify the distinction between vulnerability types, here is a comparison of physical and logical vulnerabilities:
| Vulnerability Type | Typical Examples | Impact on Business Operations |
|---|---|---|
| Physical | Unsecured server rooms, damaged cables | Can lead to unauthorised access or outages |
| Logical | Software flaws, outdated systems | Causes data breaches and workflow risks |
| Combined Threat | Both vulnerabilities exploited together | Severe disruption and regulatory penalties |
Why This Matters for Your Business
You’re running critical operations. Downtime costs money. Data breaches destroy trust and trigger regulatory penalties.
A proper vulnerability assessment tells you exactly what’s broken and gives you a roadmap to fix it—before attackers find these gaps.
This isn’t theoretical risk. Unidentified vulnerabilities lead directly to compromised systems, stolen data, and operational disruption.
Assessments also support your compliance requirements. Whether you’re meeting financial regulations or industry standards, documented security testing strengthens your compliance position.
Key Outcomes You’ll Receive
A quality assessment delivers:
- Comprehensive inventory of security weaknesses
- Risk ratings for each vulnerability
- Detailed remediation steps tailored to your environment
- Timeline recommendations for fixes based on severity
- Evidence for compliance audits and governance discussions
This actionable intelligence lets you prioritise spending on actual threats rather than guessing what might be wrong.
Below is a summary of the outcomes delivered by network vulnerability assessments:
| Assessment Outcome | Value for Engineering Firms | Value for Financial Firms |
|---|---|---|
| Inventory of Weaknesses | Protects proprietary designs | Safeguards sensitive client data |
| Risk Ratings | Prioritises system repairs | Supports compliance requirements |
| Tailored Remediation | Matches technical environments | Fits regulatory obligations |
| Audit Evidence | Demonstrates security diligence | Reduces regulatory risk |
Pro tip: Start by assessing your most critical systems—databases with client information, financial transaction systems, and engineering design repositories—then expand outward to less sensitive infrastructure.
Types of Assessments and Key Methods
Not all vulnerability assessments work the same way. The type you choose depends on your network setup, compliance requirements, and what you’re trying to discover. Understanding the difference helps you get the right insights for your business.
External vs Internal Scans
Your vulnerability assessment uses two distinct scanning approaches. External scans test your network from the outside, simulating how attackers would probe your defences. Internal scans examine systems from within your network, finding weaknesses that employees or contractors could exploit.
For a financial services firm, external scans catch vulnerabilities that expose you to the internet. Internal scans reveal risks from compromised user accounts or insider threats.
Most assessments combine both methods for complete coverage:
- External scans check firewalls, web servers, and public-facing systems
- Internal scans assess workstations, servers, databases, and network infrastructure
- Cross-comparison identifies gaps between your external and internal security posture
Commercial and Open Source Scanning Tools
Multiple scanning tools verify vulnerabilities using both commercial platforms and open-source solutions. This layered approach catches vulnerabilities that single-tool assessments might miss.
Commercial scanners offer faster processing and vendor support. Open source tools provide flexibility and transparency. A proper assessment leverages both for maximum accuracy.
Your assessment provider should use industry-standard tools that stay current with newly discovered vulnerabilities. This ensures you’re checking against the latest threat database.
Manual Verification and DNS Checks
Automated scanning finds technical weaknesses. Manual verification by security experts confirms which findings are actually exploitable versus false positives. This step matters more than you might think.
A misconfigured service might flag as vulnerable, but if it’s not actually exposed or used, it’s low risk. Expert eyes separate real threats from noise.
DNS verification ensures the scan results are legitimate and tied to your actual infrastructure. This prevents false reports and clarifies which systems are genuinely at risk.
Severity Classification and Remediation
Assessment results should tell you exactly which vulnerabilities matter most and how to fix them in order of business impact.
Your report needs customised remediation advice tailored to your specific environment. Generic recommendations don’t work when your financial systems use different software than your engineering workstations.
Severity classification typically follows:
- Critical (active exploitation risk, immediate fix required)
- High (significant exposure, fix within days)
- Medium (potential risk, plan remediation within weeks)
- Low (minimal impact, address during regular maintenance)
This prioritisation lets your team focus spending where it matters most.
Pro tip: Request a detailed remediation roadmap that accounts for your actual business operations—shutdown windows, system dependencies, and budget constraints—rather than accepting generic fixes.
Critical Steps in the Assessment Process
A proper vulnerability assessment doesn’t just happen—it follows a structured sequence that ensures accuracy, legality, and actionable results. Each step builds on the previous one to give you reliable intelligence about your network security.
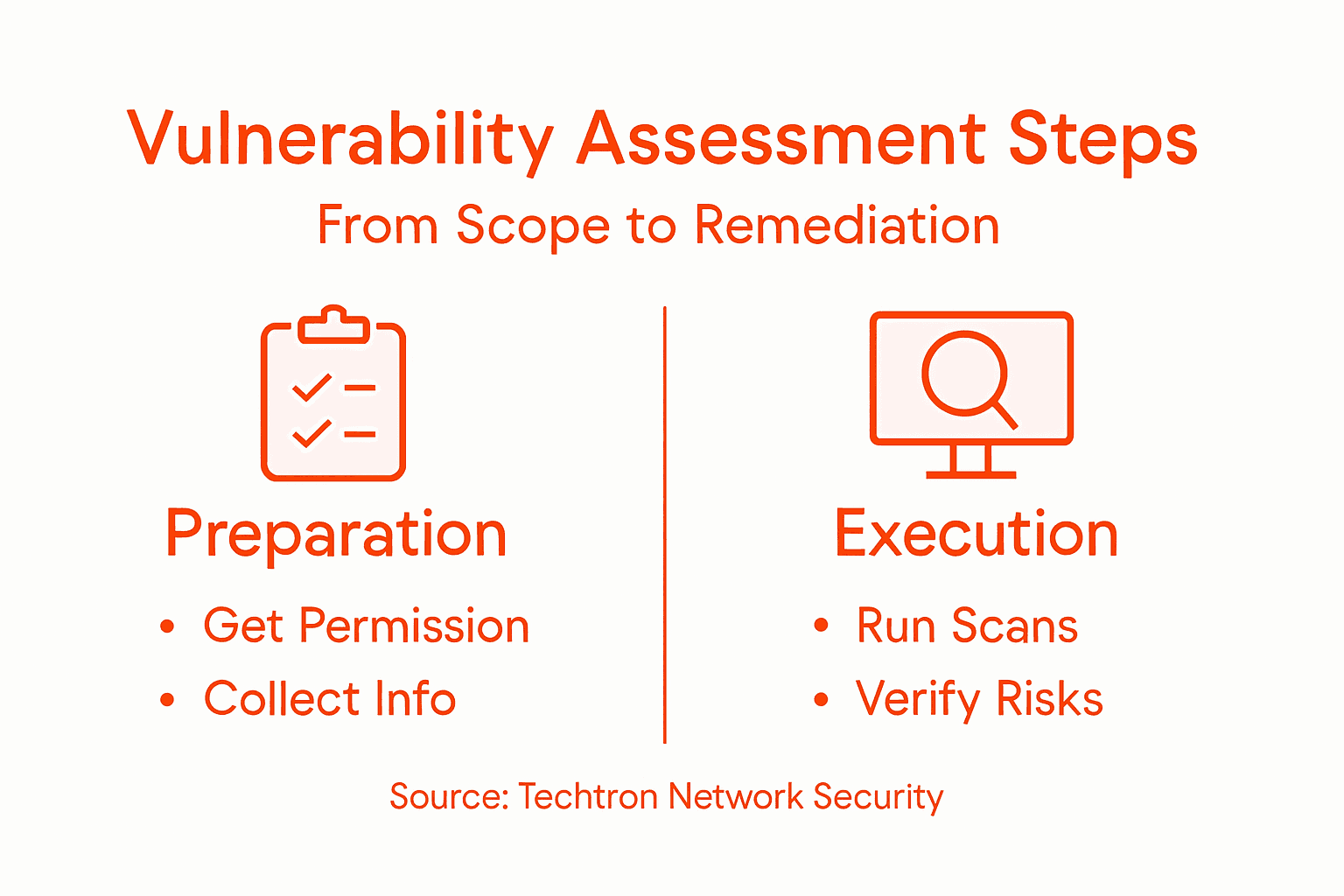
Step 1: Permission and Scope Definition
Before any scanning starts, you need explicit written permission from your organisation’s leadership. This sounds obvious, but it matters legally and operationally. Scans can temporarily impact network performance, and you need sign-off before that happens.
You’ll also define exactly what gets scanned. Your financial systems. Your engineering servers. Your backup infrastructure. Being specific prevents surprises and ensures nothing critical gets accidentally disrupted.
Document your scope clearly:
- Which systems and networks will be scanned
- Which systems are off-limits
- Scanning timeframe and duration
- Contact person if issues arise during the scan
Step 2: Information Collection
Your assessment team gathers domain names and IP address ranges that belong to your organisation. This sounds straightforward, but many companies discover undocumented systems during this phase—forgotten servers, old branch office equipment, or cloud resources nobody tracks anymore.
This inventory becomes your baseline. Everything scanned gets compared against this list so you know exactly what was assessed.
Step 3: Extensive Scanning Using Multiple Tools
Vulnerability assessment processes conduct low-intensity scans using multiple scanning tools simultaneously. Low-intensity means the scans don’t overwhelm your network—they run at a pace your systems can handle.
Multiple tools catch different vulnerability types. Tool A might find a patching gap that Tool B misses. Running both ensures comprehensive coverage.
This step takes time. Quality scans are thorough scans. Rushing this phase means missing vulnerabilities.
Step 4: Expert Verification
Automated results need manual verification by security experts. This separates real vulnerabilities from false alarms. An expert might spot that a flagged service looks exploitable but isn’t actually reachable from the network.
This expertise reduces noise and gives you results you can actually trust and act on.
Step 5: Detailed Reporting and Remediation Guidance
Your final report should tell a clear story: what was found, why it matters, and exactly how to fix it.
Quality reports include:
- Executive summary (business impact overview)
- Detailed findings with severity ratings
- Remediation steps for each vulnerability
- Timeline recommendations based on risk level
- Follow-up consultation availability
Your assessment team should offer follow-up guidance. Questions will arise. Things change. Good providers stay available to help.
Pro tip: Schedule the assessment during a period when network changes can be implemented—avoid peak trading periods for financial firms or critical project phases for engineering companies.
Ensuring POPIA and Regulatory Compliance
In South Africa, the Protection of Personal Information Act (POPIA) governs how organisations handle personal data. Network vulnerability assessments directly support your POPIA compliance by identifying security gaps that could expose personal information. Regulators expect you to demonstrate proactive security measures—assessments prove you’re taking this seriously.
Understanding Your POPIA Obligations
POPIA requires lawful processing of personal data with appropriate security controls. You must appoint an Information Officer responsible for safeguarding that data. You must conduct impact assessments to identify privacy risks. You must maintain policies, procedures, and audit trails.
A vulnerability assessment documents your security posture. It shows regulators and auditors that you’ve identified weaknesses and are addressing them.
Personal Information Impact Assessments
Personal Information Impact Assessments identify privacy risks within your systems and processes. These assessments complement network vulnerability scans by examining how personal data flows through your environment.
When your assessment identifies a vulnerability affecting systems that handle personal information, that becomes a privacy risk requiring immediate attention. Both assessments work together to paint a complete security picture.
Governance and Risk Management Frameworks
Compliance requires proper governance structures and operational controls. Your organisation needs clear policies defining who can access what data, how it’s processed, and what happens when incidents occur.
Vulnerability assessments feed directly into this framework. They reveal gaps in access controls, encryption, logging, and monitoring—all critical to demonstrating POPIA compliance.
Your framework should address:
- Data classification and handling procedures
- Access control policies aligned with assessment findings
- Incident response procedures for security breaches
- Documentation and record retention policies
- Regular security testing and assessments
Staff Training and Awareness
Compliance isn’t just technology. Your team must understand personal information protection requirements. Effective staff training supports POPIA compliance by ensuring employees know what vulnerabilities look like and how to report them.
A single mishandled email containing client data, or an employee clicking a phishing link, can undermine all your technical controls.
Regular Assessment and Monitoring
Compliance isn’t a one-time checkbox—it’s an ongoing process of identifying risks, implementing controls, and proving you’re doing both.
Conducting vulnerability assessments annually, or when your systems significantly change, demonstrates commitment to POPIA compliance. Auditors expect evidence of regular testing.
Document everything. Keep assessment reports, remediation records, and evidence that you’ve addressed findings. This documentation protects your organisation during regulatory reviews.
Building Your Compliance Evidence
Vulnerability assessments create tangible evidence that you’re taking data security seriously:
- Assessment reports showing systematic testing of systems
- Remediation records proving you fixed identified weaknesses
- Policy documents aligned with assessment recommendations
- Training records showing staff awareness
- Incident response plans informed by vulnerability findings
This evidence supports your POPIA compliance claim and reduces regulatory risk significantly.
Pro tip: Schedule your vulnerability assessment before any regulatory audit, then use the findings to drive remediation—auditors respect organisations that identify and fix issues proactively rather than waiting to be told about problems.
Mitigating Risks and Common Pitfalls
Finding vulnerabilities is only half the battle. The real work begins with fixing them systematically and avoiding mistakes that leave you exposed. Most organisations stumble not because assessments fail, but because they don’t act on the results properly.
The Human and Process Problem
Technology alone won’t save you. A holistic approach integrating technology, personnel, and processes is essential for mitigating cyber risks effectively.
Your team can have the best firewalls money can buy, but if staff don’t follow security procedures or click phishing emails, you’re still vulnerable. Training, clear policies, and accountability matter as much as technical controls.
Prioritising Vulnerabilities Correctly
Your assessment report lists dozens of findings. You can’t fix everything at once. The mistake most organisations make is treating all vulnerabilities equally.
You need to prioritise based on:
- Business impact: Which systems matter most to your operations?
- Exploitability: Can attackers actually reach and exploit this?
- Severity: How much damage would a successful attack cause?
- Effort required: Can you fix this quickly or does it need major changes?
A critical vulnerability in a rarely-used system might wait longer than a medium-risk issue affecting your primary financial system. Context matters.
Managing False Positives
Automated scans generate noise. A service might flag as vulnerable when it’s actually protected by network controls you didn’t document during the assessment. Managing false positives and addressing patch delays requires expert knowledge and continuous monitoring.
This is why manual verification by experienced security professionals matters. They distinguish between real threats and misleading alerts, preventing wasted effort on non-issues.
Patch Management Delays
Vendors don’t always release patches immediately when vulnerabilities are discovered. Sometimes they’re working on the fix. Sometimes they’re testing to ensure the patch doesn’t break other systems.
You can’t wait indefinitely. Implement interim controls while patches are pending—restricted network access, additional monitoring, or temporary process changes.
Building a Remediation Plan
Your remediation plan should be realistic about timelines, resources, and dependencies—not a wishlist of perfection that never happens.
A solid plan includes:
- Specific vulnerability assignments with owner names
- Target remediation dates based on severity
- Dependencies noted (this system can’t be patched until that one is updated)
- Success criteria (how do we know it’s fixed?)
- Fallback options if a patch breaks something
Document everything. When auditors ask if you’ve addressed findings, show them the plan and the completion records.
Ongoing Monitoring and Re-assessment
Vulnerabilities don’t stay fixed. New ones emerge constantly. Your remediation isn’t complete until you’ve verified the fixes actually work.
Schedule follow-up assessments quarterly or annually, depending on your risk profile. Re-scan critical systems more frequently. Track which vulnerabilities reappear—that signals a process problem needing attention.
Pro tip: Assign one person ownership of the remediation plan and give them authority to coordinate across departments—without a single point of accountability, fixes slip indefinitely.
Secure Your Business with Expert Network Vulnerability Assessments
The challenge every South African engineering and financial firm faces today is managing complex network vulnerabilities before they turn into costly breaches. This article highlights how a meticulous Network Vulnerability Assessment helps you identify and prioritise risks, understand physical and logical vulnerabilities, and meet POPIA compliance demands. The stakes are high with sensitive client data and proprietary designs at risk. Without clear, expert-led remediation, your business could suffer operational disruption or regulatory penalties.
At Techtron, we understand these pressures and offer customised network security and managed IT services tailored for your industry. Our specialists combine advanced automated scanning with thorough manual verification to deliver accurate vulnerability reports plus practical remediation roadmaps. We support your ongoing compliance with POPIA while reducing your technical burden through co-managed or fully managed services.
Take control of your network security today. Partner with us to transform vulnerability findings into decisive actions and safeguard your business continuity. Visit Techtron now to learn how our comprehensive IT solutions can minimise your risks and keep your operations secure.
Frequently Asked Questions
What is a network vulnerability assessment?
A network vulnerability assessment is a systematic process that identifies, classifies, and documents security weaknesses in your IT infrastructure, helping you find potential points of attack before they can be exploited by cybercriminals.
Why do businesses need network vulnerability assessments?
Businesses need network vulnerability assessments to proactively identify security gaps, mitigate risks before data breaches occur, ensure compliance with regulations, and protect their sensitive information from unauthorized access.
What are the key outcomes of a network vulnerability assessment?
Key outcomes of a network vulnerability assessment include a comprehensive inventory of security weaknesses, risk ratings for each vulnerability, detailed remediation steps tailored to your environment, and evidence for compliance audits.
How often should network vulnerability assessments be conducted?
Network vulnerability assessments should be conducted regularly, such as annually or whenever significant changes to your systems occur. For critical systems, more frequent assessments are recommended to ensure ongoing security.