
Staff cybersecurity training guide for IT managers
TL;DR:
- Staff training is the most effective defense against cyber threats and phishing attacks.
- Building a proactive, organization-wide security culture requires ongoing, measurable awareness programs.
- Involving leadership and HR ensures training aligns with firm culture and promotes genuine behavioral change.
Your staff are the most exploited entry point in your firm’s defences. Not your firewall, not your cloud configuration. Your people. Phishing simulations can reduce baseline risks by up to 86% within 12 months, which means the single most effective security investment you can make is not software. It is training. For IT managers at South African professional service firms, this guide breaks down exactly how to build, run, and sustain a staff cybersecurity training program that changes real behaviour and measurably reduces your firm’s exposure.
Key Takeaways
| Point | Details |
|---|---|
| Training is essential | Staff-focused cybersecurity training significantly reduces the risk of data breaches and phishing attacks. |
| Culture is key | Building a true cybersecurity culture requires leadership, HR involvement, and consistent behavioral reinforcement. |
| Measure and adapt | Monitor staff engagement and threat metrics to continuously improve your training program. |
| Use multiple methods | Combine simulated phishing, microlearning, and routine refreshers for the best results in staff awareness. |
Understanding the stakes: Why staff training matters
Cyber threats have grown more targeted, more automated, and far harder to filter at the network level. The uncomfortable reality is that most successful breaches do not start with a sophisticated zero-day exploit. They start with someone in your accounts department clicking the wrong link.
Phishing is the leading attack method targeting organisations’ weakest link: their staff. Attackers know that it is far easier to trick a busy professional into revealing credentials than it is to crack a well-configured server. Social engineering, pretexting, and business email compromise (BEC) are all methods designed to exploit human trust, not technical vulnerabilities.
For South African professional service firms, the threat is not abstract. Financial advisory firms, engineering consultancies, and legal practices all handle sensitive client data and process significant financial transactions. That makes them attractive targets. Local firms also face a maturing threat landscape from both international cybercrime groups and increasingly capable local actors.
The security training benefits extend well beyond compliance. When staff genuinely understand what a phishing email looks like, why they should never use public Wi-Fi for client work, and how to report suspicious activity, your firm’s entire risk profile changes. Training shifts the dynamic from reactive incident response to proactive threat avoidance.
“The goal of security awareness training is not just to inform. It is to change the decisions people make under pressure, when an attacker is counting on them to act fast and think slow.”
Here are the core risk areas that proper training addresses directly:
- Phishing and spear phishing: Targeted emails impersonating trusted parties
- Business email compromise: Attackers spoofing or hijacking executive email accounts to authorise fraudulent payments
- Password hygiene: Weak or reused credentials that expose multiple systems at once
- Removable media risks: USB drives and external devices as malware delivery mechanisms
- Shadow IT: Staff using unapproved apps or cloud services that fall outside your security controls
Real behavioural change is the goal here. Compliance checkbox training, where staff watch a 20-minute video once a year and click “complete,” does not achieve this. Your program needs to be ongoing, contextual, and tied to measurable outcomes.
Now that we have established why training is essential, let us look at what you need to get started.
Laying the groundwork: Building your training program
Understanding the threat landscape is the first step. Now let us map out what you will need before taking action.

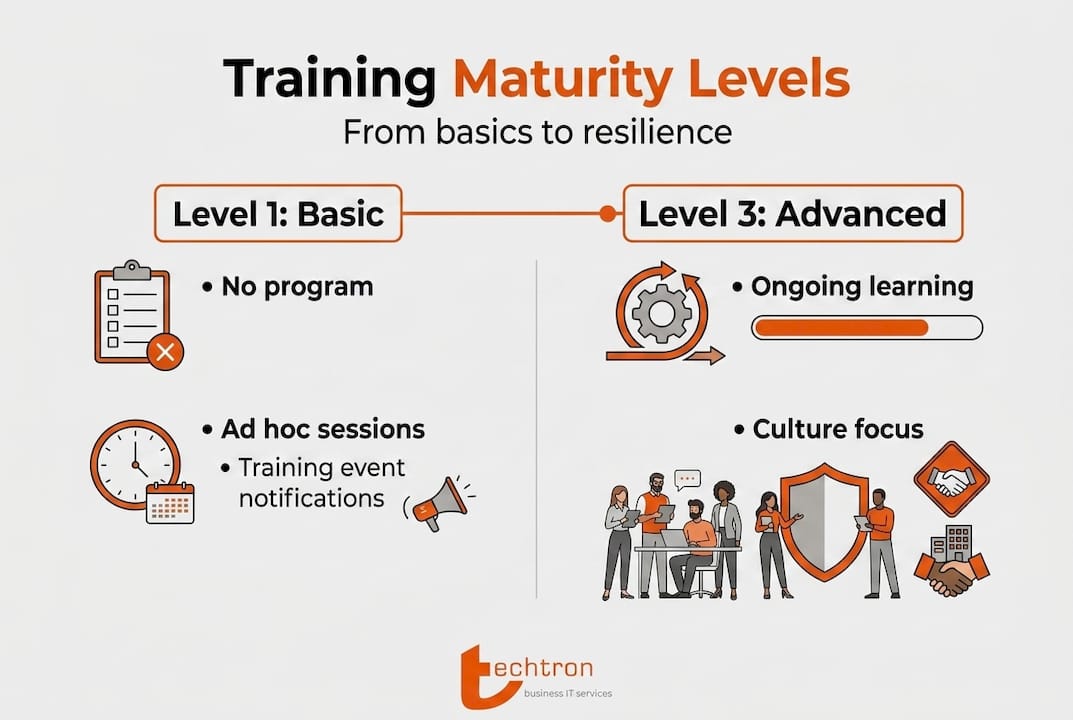
Before you schedule a single training session, you need to assess where your organisation currently sits on the security awareness spectrum. The SANS Maturity Model provides an actionable roadmap for security programs, focusing on behaviours and culture rather than just knowledge transfer. It describes five levels, from non-existent awareness at Level 1 through to an embedded security culture at Level 5.
Most mid-sized South African professional service firms sit somewhere between Level 2 (compliance-focused) and Level 3 (programme-driven). Your goal should be reaching Level 4, where training is proactive and staff actively contribute to the firm’s security posture.
| Maturity level | Description | Key indicator |
|---|---|---|
| Level 1: Non-existent | No formal awareness efforts | Staff cannot identify a phishing email |
| Level 2: Compliance-focused | Annual checkbox training | Low engagement, high click rates on simulations |
| Level 3: Programme-driven | Regular training with some metrics | Declining phish-prone rates over time |
| Level 4: Proactive | Staff report threats and ask questions | Incident reporting rates increase |
| Level 5: Embedded culture | Security is a shared value | Low incident rates, high engagement |
Getting HR and internal communications involved early is not optional. It is essential. Your HR team controls onboarding, performance frameworks, and internal communications channels. They can embed security habits into new staff orientation, include security behaviours in performance reviews, and ensure your messaging reaches people in formats they actually consume.
Aligning your training content with the real risk scenarios your firm faces is equally important. A financial advisory firm needs very different scenarios than a construction engineering consultancy. The training content should reflect your firm’s actual workflows, clients, and threat vectors.
Pro Tip: Start with microlearning modules of 5 to 10 minutes each rather than lengthy courses. Research consistently shows that shorter, frequent learning sessions drive better retention and completion rates than long annual courses. The innovative IT solutions available today make this easier than ever to deliver at scale.
When setting your training goals, make them specific and measurable. “Improve security awareness” is not a goal. “Reduce phish-prone percentage from 28% to below 10% within 12 months” is a goal you can track, report on, and build a program around.
Executing your cybersecurity training: Essential methods and tools
With your foundation set, you can now begin implementing proven training tactics.
Not all training methods deliver equal results. Choosing the right mix for your team size, budget, and risk profile is critical. The table below compares the most common delivery methods available to mid-sized firms.
| Training method | Best for | Key benefit | Limitation |
|---|---|---|---|
| Simulated phishing | All staff | Direct behaviour measurement | Must be followed by learning, not punishment |
| Self-paced e-learning | Flexible schedules | Scalable and cost-effective | Low engagement if content is generic |
| Live workshop sessions | High-risk roles | Deep engagement and Q&A | Time-intensive and costly to scale |
| Ongoing campaigns | All staff | Keeps security top-of-mind | Requires consistent content refresh |
| Gamified platforms | Younger or tech-savvy teams | High completion and retention | May not suit all firm cultures |
Phishing simulations are the single most powerful tool in your training toolkit. When run correctly, phishing simulations drop phish-prone rates from 33.1% to 4.1% over a 12-month period. That is a dramatic reduction in real-world risk. The key word is “correctly.” A simulation that catches someone and embarrasses them publicly will damage trust and reduce reporting. A simulation that catches someone and immediately delivers a short, supportive learning moment will change behaviour.
Here is how to run an effective training cycle for a mid-sized professional service firm:
- Baseline assessment: Run your first phishing simulation before any formal training to establish your starting phish-prone rate. This is your benchmark.
- Launch core e-learning modules: Cover the essentials first. Password management, phishing recognition, safe browsing, and device security.
- Schedule phishing simulations monthly: Vary the type, urgency level, and sender profile. Mix obvious attempts with sophisticated ones.
- Deliver targeted follow-up training: Staff who click on simulations receive immediate, brief learning content. Not blame. Learning.
- Run quarterly refresher campaigns: Use newsletters, posters, or short video clips to keep threats and habits visible between formal training sessions.
- Review and report monthly: Track your phish-prone rate, module completion, and incident reports. Share results with management and HR.
Review cybersecurity training frequency guidelines to decide on the right cadence for your firm’s risk level. For most professional service firms, monthly simulations and quarterly structured training deliver the best results without creating security fatigue.
Pro Tip: Rotate your phishing simulation templates regularly. If staff see the same style of fake email repeatedly, they learn to recognise your simulations rather than developing genuine threat detection skills. Real attackers do not use the same template twice. Your awareness training programs should reflect that unpredictability.
Security fatigue is a genuine risk. If staff feel constantly surveilled, blamed for mistakes, or overwhelmed by security messaging, engagement drops sharply. Balance your training cadence with positive reinforcement, celebrate staff who report phishing attempts, and make security feel like a team effort rather than a compliance burden.
Verifying results and sustaining a security culture
Having rolled out your training, it is essential to ensure the results last and grow over time.
Measurement is where many programs stall. You run the training, the numbers look better, and then six months later your phish-prone rate creeps back up because the program lost momentum. Sustaining a security culture requires ongoing measurement and continuous reinforcement.
The metrics that matter most are not just completion rates. Those tell you who watched the video, not who changed their behaviour. Track these instead:
- Phish-prone percentage (PPP): The percentage of staff who click on simulated phishing emails. This is your most direct behavioural measure.
- Incident report rate: How often are staff proactively reporting suspicious emails, calls, or behaviours? A rising report rate is a strong sign of genuine culture change.
- Time to report: How quickly do staff flag suspicious activity? Faster reporting means faster response and less damage.
- Module completion and re-attempts: Completion alone is weak data, but combined with re-attempt rates on failed quiz questions, it reveals where knowledge gaps persist.
- Near-miss and incident data: Track actual security incidents and near-misses. Are they decreasing in frequency or severity over time?
Behavioural change, not just knowledge, is the real goal of a mature cybersecurity program. A staff member who knows what phishing is but still clicks a link under pressure has not been trained effectively.
Leadership visibility matters enormously here. When a firm’s managing director mentions cybersecurity in a team meeting, forwards a phishing warning from IT, or participates in a simulation alongside staff, the message lands differently. It signals that security is a firm-wide priority, not just an IT department concern.
Refresh your content regularly. Threat actors change their tactics constantly. The pretexting scenarios from 18 months ago are already outdated. Quarterly content reviews ensure your training reflects current threats, which keeps staff genuinely challenged rather than pattern-matching against familiar examples.
Celebrate wins clearly and publicly. When a staff member correctly identifies and reports a sophisticated phishing attempt, acknowledge it. When your firm completes a quarter with zero successful phishing clicks, share that milestone. Good cyber hygiene best practices are built on positive reinforcement, not just consequence.
HR can support this through structured recognition programs, including security behaviour as a positive note in performance reviews, and ensuring that security awareness is woven into the onboarding process for every new hire. Training is not a once-off event. It is an ongoing organisational habit.
What most cybersecurity training guides miss
Most training guides treat cybersecurity awareness as an IT problem with an IT solution. Deploy the platform, run the simulations, track the numbers, report to management. Done.
That approach produces compliance. It does not produce resilience.
In our experience working with professional service firms, the programs that fail are almost always the ones where IT owns training alone. No HR involvement. No leadership champion. No connection to the firm’s values or culture. Staff complete modules because they have to, not because they understand why it matters.
True transformation happens when training is organisational, not just individual. That means your managing partner needs to talk about security. Your HR team needs to include it in performance conversations. Your operations manager needs to ask about it in project reviews.
The other thing guides often overlook is the emotional dimension of security mistakes. When someone clicks a phishing link, they feel embarrassed and exposed. If your program responds with blame or public shaming, they will hide future mistakes instead of reporting them. A culture where reporting a near-miss is celebrated as a win is far more secure than one where staff conceal errors out of fear.
Microlearning works because it meets people where they are. Short, scenario-based modules delivered at the moment of risk, like a brief reminder before a staff member downloads an attachment from an unknown sender, are dramatically more effective than annual awareness days. Pair that with improving business cybersecurity at the infrastructure level, and you build layered defences that actually hold.
The hardest part of all this is patience. Culture change takes 18 to 24 months of consistent effort. Most firms abandon programs after three to four months because they have not seen dramatic results. Stay the course. The data is clear, and the firms that commit to ongoing programs are the ones that stop appearing in breach headlines.
Partner with TECHTRON for lasting cybersecurity impact
Running a structured, measurable cybersecurity training program is demanding work, especially for IT managers who are already stretched across infrastructure, helpdesk, and compliance obligations. TECHTRON offers managed IT services specifically designed for South African professional service firms, including tailored staff awareness training, phishing simulation management, and ongoing security culture support. Find out how exposed your firm really is with a business cyber security review, or explore our free cybersecurity training resources to get started without delay. Your people can become your strongest defence. Let us help you get there.
Frequently asked questions
How often should staff receive cybersecurity training?
For maximum effect, staff should train at least quarterly, with monthly phishing simulations in between. Frequent, consistent training aligns directly with better and sustained risk reduction outcomes.
What are the key elements of a strong cybersecurity training program?
A strong program includes regular simulated phishing attacks, practical real-world scenarios, clear and tracked metrics, and active leadership support. The SANS model confirms that mature programs focus on measurable behaviour change rather than knowledge alone.
How can we measure the success of cybersecurity training?
Success is measured by tracking reduced risky behaviours, primarily through falling phishing simulation click rates over time and rising voluntary incident reporting rates.
Should cybersecurity training be tailored for South African businesses?
Yes, local context matters significantly. South African firms face specific compliance obligations under POPIA, as well as local threat actors and sector-specific risks that generic global training content does not adequately address.
Who should be involved in creating the training program?
IT, HR, and firm leadership must all be involved. HR and leadership buy-in is the critical factor that separates programs which drive genuine culture change from those that only produce compliance records.