
Email security in SA 2026: 85% cyberattack defense guide
Email remains the primary gateway for cyberattacks targeting South African businesses. Over 85% of cyberattacks targeting South African businesses start with compromised email, exposing mid-sized engineering and financial firms to devastating financial losses, regulatory penalties, and reputational damage. This guide reveals the most dangerous email threats facing your organization, clarifies POPIA compliance requirements, and delivers actionable technical controls that reduce phishing risks by more than 80%. You’ll learn how layered defenses, employee training, and rapid incident response protect sensitive client data while ensuring regulatory adherence in 2026’s threat landscape.
Key takeaways
| Point | Details |
|---|---|
| Email attacks dominate | 85% of cyberattacks in South Africa involve email as the primary attack vector, making it the most critical security priority. |
| Layered defenses work | Multi-factor authentication and DMARC protocols reduce account compromise and spoofing by over 80%. |
| POPIA mandates protection | POPIA mandates protection of personal information transmitted via email with substantial penalties for non-compliance. |
| Training cuts phishing success | Regular employee awareness programs reduce phishing success rates by approximately 70%. |
| Fast response limits damage | Fast incident response reduces downtime from days to hours and supports compliance obligations. |
Introduction to email security importance
Email security forms the cornerstone of cybersecurity strategy for mid-sized South African engineering and financial firms. Email accounts are targeted more than other attack vectors in SA because they provide direct access to sensitive client information, financial data, and intellectual property. A single successful breach can cost your organization millions in ZAR through operational disruptions, regulatory fines, legal liability, and customer trust erosion.
The financial impact extends beyond immediate remediation costs. Firms face prolonged downtime while security teams contain threats, investigate breach scope, and restore compromised systems. Client relationships suffer when confidential engineering designs or financial records are exposed, leading to contract cancellations and competitive disadvantages. Regulatory bodies increasingly scrutinize email security controls, with POPIA enforcement creating legal obligations that demand proactive protection measures.
South African firms operating in engineering and financial sectors face unique pressures. You handle highly sensitive client data daily, from proprietary building designs to personal financial information subject to strict privacy laws. Your email infrastructure serves as the primary communication channel for these critical exchanges, making it an attractive target for sophisticated threat actors seeking valuable intellectual property or financial gain.
Implementing multi-factor authentication solutions represents one essential layer in comprehensive email protection. However, effective security requires understanding the full threat landscape, regulatory requirements, and proven technical controls that work together to create resilient defenses. The following sections examine specific threats targeting South African firms and practical strategies to counter them.

Common email security threats in South African firms
Phishing attacks represent the dominant email security threat facing mid-sized firms. Phishing represents over 60% of email incidents in SA financial firms, with attackers crafting increasingly sophisticated messages that mimic legitimate business communications. These attacks exploit human psychology rather than technical vulnerabilities, making them particularly difficult to prevent through technology alone.
Spear phishing takes this threat further by targeting specific individuals within your organization. Attackers research executives, finance staff, and IT managers through social media and public records, then craft personalized messages that reference actual projects, clients, or colleagues. A finance manager might receive an urgent request from a spoofed CEO email address requesting an immediate wire transfer, complete with realistic context about a pending deal.
Malware attachments and malicious links continue plaguing South African engineering firms. Attackers disguise ransomware as project files, invoices, or compliance documents. Once opened, these files encrypt critical systems and demand payment for data recovery. One mid-sized Cape Town engineering firm experienced this firsthand:
“Our project manager opened what appeared to be updated building specifications from a regular client. Within hours, our entire file server was encrypted. We lost access to active project files for three days while our IT team worked to restore from backups. The incident cost us over R500,000 in lost productivity and emergency response fees.”
Email spoofing exploits weaknesses in email authentication protocols. Attackers forge sender addresses to impersonate trusted partners, clients, or internal staff. Without proper email security best practices and technical controls, recipients have no way to verify message authenticity. Financial firms face particular risk from business email compromise schemes where attackers intercept legitimate email threads, then inject fraudulent payment instructions that appear to come from known vendors.
The sophistication of these threats continues escalating. Attackers now use artificial intelligence to analyze writing styles and create convincing impersonations. They monitor email patterns to time attacks when staff are rushed or distracted. Email threat mitigation for engineering firms requires understanding these evolving tactics and implementing layered defenses that address both technical and human vulnerabilities.
Regulatory compliance and legal requirements for email security
The Protection of Personal Information Act establishes strict obligations for South African organizations handling personal data through email communications. POPIA requires firms to implement appropriate technical and organizational measures protecting personal information against unauthorized access, loss, or damage. Email systems transmitting client names, financial details, identification numbers, or health information fall squarely under these requirements.
Compliance mandates extend beyond basic encryption. You must ensure:
- Data minimization in email communications, sharing only necessary personal information
- Access controls limiting who can send, receive, or archive sensitive emails
- Retention policies that automatically delete personal data when no longer required
- Audit trails documenting email access and modifications for accountability
- Breach notification procedures that alert affected individuals within legal timeframes
Penalties for inadequate email security have increased substantially. The Information Regulator can impose administrative fines up to R10 million for serious POPIA violations. Beyond financial penalties, firms face civil lawsuits from affected individuals, criminal charges in cases of intentional non-compliance, and reputational damage that erodes client trust and competitive position.
Financial services firms face additional obligations under sector-specific regulations. The Financial Intelligence Centre Act requires monitoring and reporting suspicious email communications that might indicate money laundering or terrorist financing. Engineering firms working on government projects must meet security clearance requirements that include email protection standards.
These regulatory pressures drive email security investments across South African mid-sized firms. POPIA compliance and email security integration helps you meet legal obligations while simultaneously strengthening defenses against cyber threats. Compliance should be viewed as a baseline rather than a ceiling, with best-in-class firms implementing controls that exceed minimum requirements to better protect client interests and business operations.
Email security technologies and best practices
Multi-factor authentication blocks the vast majority of account compromise attempts targeting email systems. MFA reduces account compromise risk by 90% by requiring users to verify identity through multiple factors beyond passwords alone. Implementation typically combines something users know (password), something they have (mobile device or security token), and sometimes something they are (fingerprint or facial recognition).
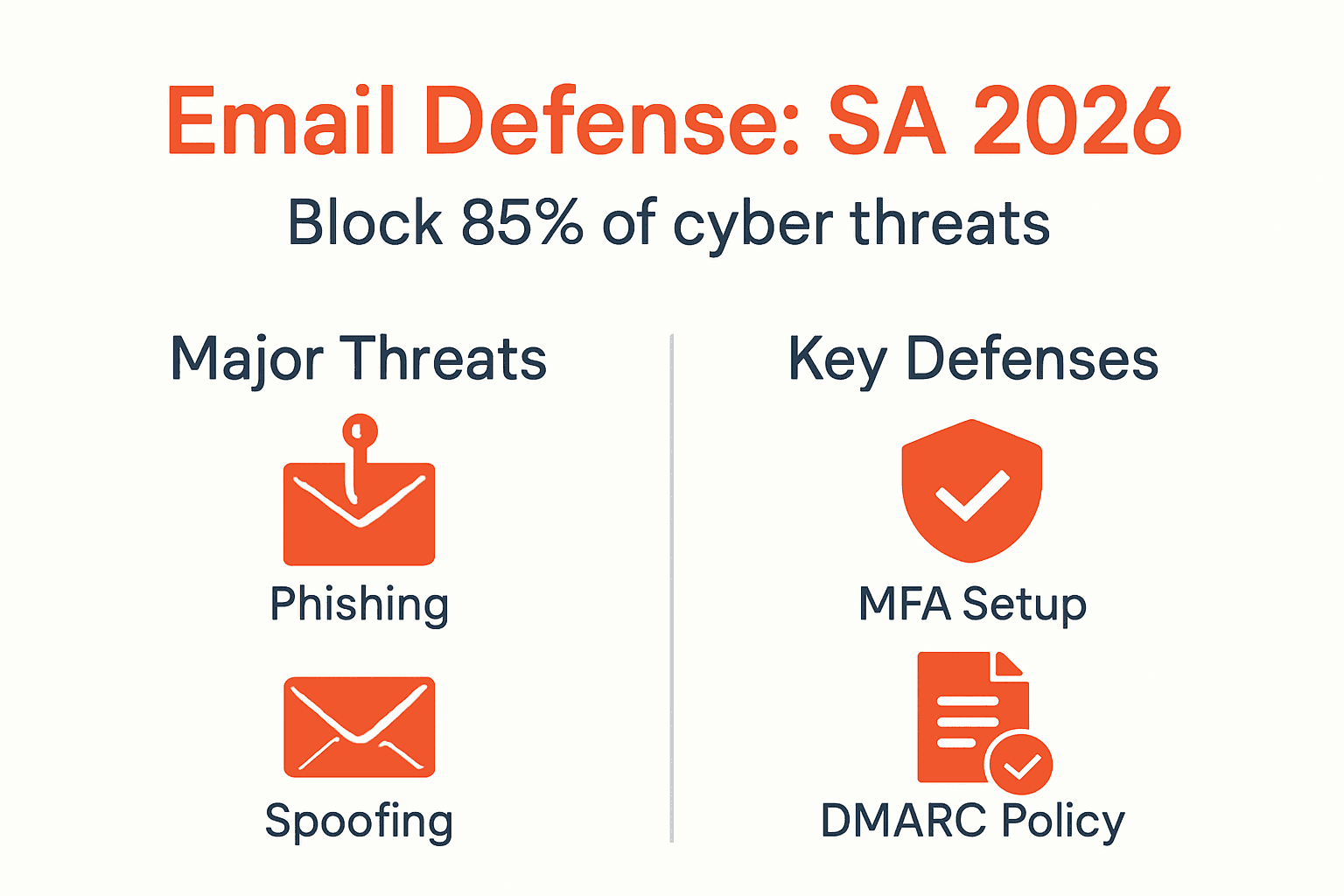
DMARC implementation provides powerful protection against email spoofing and phishing. Domain-based Message Authentication, Reporting, and Conformance protocols verify that incoming messages actually originate from claimed sender domains. DMARC cuts spoofing by 80% by rejecting fraudulent messages before they reach user inboxes. You configure DMARC records in your DNS settings, specifying how receiving servers should handle unauthenticated messages.
Secure email gateways provide another critical defense layer. These solutions scan incoming messages for malware, phishing indicators, and policy violations before delivery. Advanced gateways use machine learning to detect zero-day threats and sophisticated social engineering attempts that traditional spam filters miss. They also enforce data loss prevention policies, blocking outbound emails containing sensitive information sent to unauthorized recipients.
User training remains essential despite technical controls. Regular phishing simulations and awareness programs teach employees to recognize suspicious messages, verify requests through alternative channels, and report incidents promptly. Training effectiveness increases when programs include:
- Monthly phishing simulations with immediate feedback for users who click malicious links
- Quarterly security awareness sessions covering current threat trends and real incident examples
- Clear reporting procedures that encourage employees to flag suspicious emails without fear of blame
- Executive participation demonstrating organizational commitment to security culture
Pro Tip: Combine automated phishing simulations with personalized coaching for employees who repeatedly fail tests. One-on-one sessions addressing specific knowledge gaps prove more effective than generic training materials.
The following table compares key effective email security technologies and their primary benefits:
| Technology | Primary Function | Risk Reduction |
|---|---|---|
| Multi-Factor Authentication | Prevents unauthorized account access | 90% reduction in compromises |
| DMARC/SPF/DKIM | Blocks email spoofing and impersonation | 80% reduction in spoofing |
| Secure Email Gateways | Filters malware and phishing messages | 70% reduction in malicious emails |
| User Training Programs | Reduces human error and improves threat recognition | 70% reduction in phishing success |
| Email Encryption | Protects message content during transmission | 100% protection of intercepted messages |
Implementing best email security practices requires layered defenses combining these technologies with strong policies. No single control provides complete protection, but integrated systems create multiple barriers that dramatically reduce successful attack probability. Consider starting with MFA and DMARC as foundational controls, then adding gateway solutions and training programs to strengthen your overall security posture.
Understanding cybersecurity basics helps contextualize these email-specific controls within broader organizational security frameworks. Email protection works best when integrated with endpoint security, network monitoring, and incident response capabilities.
Common misconceptions about email security
Many South African firms mistakenly believe spam filters provide adequate protection against modern email threats. Spam filters alone block less than 50% of targeted phishing emails specifically crafted to bypass automated detection. Traditional filters rely on known threat signatures and pattern matching, struggling with novel attacks or messages tailored to specific organizations and individuals.
The assumption that technical controls eliminate human factors represents another dangerous misconception. Even with sophisticated gateway solutions and authentication protocols, employees remain the final defense layer. Attackers increasingly focus on social engineering precisely because it exploits human psychology rather than technical vulnerabilities. A moment of distraction or urgency can lead staff to bypass security warnings or share credentials despite robust technical protections.
Some organizations underestimate the value of employee training, viewing it as a checkbox compliance exercise rather than a critical security investment. Research demonstrates that regular, engaging awareness programs reduce phishing success rates by approximately 70%. Training effectiveness depends on quality and consistency rather than one-time annual sessions. Interactive simulations with immediate feedback prove far more impactful than passive video presentations.
The following comparison illustrates how misconceptions differ from security realities:
| Misconception | Reality |
|---|---|
| Spam filters stop all threats | Advanced phishing bypasses 50%+ of filters |
| Antivirus protects email attachments completely | Zero-day malware evades signature-based detection |
| Strong passwords alone secure accounts | Password-only authentication fails against common attacks |
| Security is IT’s responsibility exclusively | Effective defense requires organization-wide participation |
| Small firms aren’t targeted | Attackers specifically seek under-protected mid-sized organizations |
Another prevalent myth suggests that email encryption solves all security concerns. While encryption protects message content during transmission, it does nothing to prevent phishing, verify sender authenticity, or block malware attachments. Encrypted emails from compromised accounts still pose significant risks. Comprehensive protection requires multiple complementary controls addressing different attack vectors.
Some IT managers believe their current email security is adequate simply because they haven’t experienced a successful breach. This survivorship bias ignores unsuccessful attacks that security controls blocked and sophisticated breaches that remain undetected. Professional penetration testing and security audits often reveal vulnerabilities in systems that organizations assumed were secure.
Pro Tip: Schedule annual third-party security assessments to identify gaps in your email defenses before attackers exploit them. External experts bring fresh perspectives and knowledge of emerging threats that internal teams might miss.
Addressing these email security myths requires ongoing education and honest assessment of your organization’s actual risk exposure. Challenge assumptions by testing defenses through simulated attacks, reviewing incident data from similar firms, and staying informed about evolving threat tactics targeting your industry sector.
Incident response and business continuity after email security breaches
Prepared incident response plans dramatically reduce the operational and financial impact when email security breaches occur. Organizations with documented procedures contain threats faster, minimize data exposure, and restore normal operations more quickly than those reacting without established protocols. Your plan should clearly assign roles, define communication channels, and specify technical response steps for different breach scenarios.
Speed matters critically in breach response. Each hour of delay allows attackers to access additional systems, exfiltrate more data, or spread malware deeper into your infrastructure. Rapid detection and containment limit the breach scope, reducing remediation costs and compliance penalties. Regular testing ensures response teams can execute procedures smoothly under pressure rather than figuring out steps during an active incident.
Effective incident response includes these essential steps:
- Immediate isolation of compromised accounts and systems to prevent threat spread
- Evidence preservation documenting the attack timeline, affected systems, and data accessed
- Threat eradication removing malware, closing vulnerabilities, and forcing password resets
- System restoration from clean backups after verifying threat removal
- Stakeholder notification informing affected parties, regulators, and law enforcement as required
- Post-incident analysis identifying security gaps and implementing preventive improvements
Pro Tip: Maintain offline backup copies of critical email data to ensure recovery options even if primary systems and cloud backups are compromised. Test restoration procedures quarterly to verify backup integrity and team proficiency.
POPIA compliance requires specific breach response actions. You must notify the Information Regulator and affected individuals when breaches involve personal information, typically within 72 hours of discovery. Delayed or inadequate notification triggers additional penalties beyond those for the initial security failure. Your response plan should include pre-drafted notification templates and clear escalation criteria.
Maintaining communication integrity after email breaches presents unique challenges. Clients and partners may question whether messages actually come from your organization or represent additional attack attempts. Establish alternative communication channels through verified phone contacts or secure client portals. Transparently acknowledge the incident while demonstrating concrete remediation steps to rebuild trust.
Incident response best practices emphasize preparation over reaction. Organizations that invest in planning, testing, and training before breaches occur recover faster and experience fewer lasting impacts than those scrambling to respond without preparation. Consider incident response as essential insurance against the inevitable email security challenges facing all modern organizations.
Conclusion and practical steps for IT managers
Email security demands immediate attention from IT managers in mid-sized South African engineering and financial firms. The statistics are clear: email represents the primary attack vector in 85% of cyberattacks, and inadequate protection exposes your organization to massive financial, legal, and reputational consequences. However, proven technical controls and organizational practices dramatically reduce these risks when implemented systematically.
Begin strengthening your email security posture through these actionable steps:
- Deploy multi-factor authentication across all email accounts within the next 30 days to eliminate 90% of account compromise risks
- Implement DMARC protocols with enforcement policies rejecting unauthenticated messages claiming to originate from your domains
- Establish monthly phishing simulation and training programs with personalized coaching for employees who demonstrate vulnerability
- Review and update email security policies ensuring alignment with current POPIA requirements and industry best practices
- Develop comprehensive incident response plans with clearly assigned roles, tested procedures, and verified backup recovery capabilities
- Schedule quarterly security assessments evaluating email defense effectiveness and identifying emerging vulnerabilities
Layered defenses combining technical controls with human awareness create resilient protection that adapts to evolving threats. No single technology provides complete security, but integrated systems with multiple barriers force attackers to overcome numerous obstacles before successfully compromising your organization.
Prioritize quick wins that deliver immediate risk reduction while building toward comprehensive long-term security architecture. MFA implementation and DMARC configuration can be completed within weeks, providing substantial protection improvements with relatively modest effort. Use these early successes to build momentum for more complex initiatives like advanced gateway deployment and security culture development.
Remember that email security is not a one-time project but an ongoing operational requirement. Threats evolve continuously, requiring regular updates to defenses, policies, and training content. Allocate sufficient budget and staff time for security maintenance, monitoring, and improvement activities that sustain protection effectiveness over time.
Enhance your email security with Techtron
Protecting your organization’s email infrastructure requires specialized expertise and ongoing vigilance that internal IT teams often struggle to maintain alongside daily operational responsibilities. Techtron delivers comprehensive co-managed IT solutions specifically designed for mid-sized South African engineering and financial firms seeking enterprise-grade security without enterprise-scale IT departments.
Our cybersecurity services in South Africa include advanced email protection technologies, POPIA compliance support, and 24/7 monitoring that detects and responds to threats before they impact your operations. We handle the complex technical implementation while working alongside your team to build security awareness and incident response capabilities. Contact Techtron today to discuss how our tailored approach strengthens your email security posture and protects the sensitive data your clients trust you to safeguard.
FAQ
What are the most common email security threats faced by South African firms?
Phishing and spear phishing attacks dominate the threat landscape, accounting for over 60% of email security incidents in South African financial firms. Malware attachments disguised as legitimate business documents and email spoofing techniques that impersonate trusted contacts are also rising threats. Engineering firms face particular risk from targeted attacks seeking proprietary designs and intellectual property.
How does POPIA influence email security requirements?
POPIA mandates that organizations implement appropriate technical and organizational measures protecting personal information transmitted through email systems. The law requires access controls, encryption, audit trails, and breach notification procedures for emails containing personal data. Non-compliance can result in administrative fines up to R10 million, civil lawsuits, and criminal charges in serious cases.
What practical steps can mid-sized firms take to improve email security?
Implement multi-factor authentication to prevent 90% of account compromises and deploy DMARC protocols blocking spoofed messages. Establish secure email gateways filtering malware and phishing attempts before they reach user inboxes. Conduct regular employee training through phishing simulations and awareness programs that reduce human error by approximately 70%. Develop and test incident response plans ensuring your team can quickly contain and recover from security breaches.
Recommended
- Cybersecurity in South Africa | TECHTRON
- Cybersecurity Best Practices | TECHTRON
- Cybersecurity Best Practices 2025 | TECHTRON
- Email Security – Reliable Protection | TECHTRON
- The Ultimate Guide to Automation Tools for 2025: LinkedIn & Email Marketing – Sales Label IT Consulting
- Event Planning Security Explained: Protecting Retreats – WhenNOT Blog